Chedot is a Chromium-based Browser that replaces your default System Internet Browser. This browser offers users tools for downloading videos, faster browsing, and custom searches.
From the publisher: A feature of our browser is a high speed on slow computers, high speed download on a poor internet, support resuming file download when connection is broken and the download in multiple threads, the ability to go on blocked websites and downloading videos from video sites.
While this may seem interesting and good at start, this browser has been marked as a Potentially Unwanted Program. It monitors user activity, collects web traffic data, and user information. While using Chedot you may see additional ads throughout your browsing sessions.
About Potentially Unwanted Applications
Exactly what is a Potentially Unwanted Program (PUP)?
People have encountered it – you download a free software, you then discover some unwanted applications on your computer system or discover a strange toolbar has been included with your browser. You didn’t have them installed, so how did they appear? These unwanted applications, which are called Potentially Unwanted Programs, or PUP in short, usually tag along as a software bundle when downloading the application and could cause serious problems for computer users.
PUP does not involve malware in the traditional sense. What normally makes a PUP different from malicious software is the fact that when you download one, you’re doing it with your consent – although in most cases unintentionally and reluctantly. But, there is no doubt that PUPs remain bad news for computer users as it can be incredibly damaging to the PC in many ways.
How do unwanted programs affect you?
Unwanted programs come in many forms. More commonly, they will be found in adware bundlers which are known to utilize aggressive and misleading advertising. The majority of bundlers install many adware applications from a number of vendors, each of which features its own EULA policy. Safebytes Anti-malware completely removes this threat and safeguards your PC against PUP or malware infection. PUPS also appear in the form of undesirable toolbars or internet browser plug-ins. Not just they needlessly use up space on your screen, toolbars can also manipulate search results, track your web browsing activities, decrease your internet browser’s performance, and slow down your web connection to a crawl.
They could seem harmless but PUPs are generally spyware. They may include dialers, keyloggers, and also other software built inside them that could monitor you or send out your sensitive information to 3rd parties. Because of this unwanted program, your application may freeze, your security protections can get disabled that could leave your computer susceptible, your system could get ruined, and this list goes on and on.
Tips for preventing PUPs
• Study cautiously prior to agreeing to the license agreement as it could have a clause about PUPs.
• Always opt for the custom if you are given an option between Recommended and Custom Installations – never click Next, Next, Next thoughtlessly.
• Install an advert blocker/pop-up blocker; Deploy anti-malware products such as Safebytes Anti-malware. These software programs will establish a wall between the computer and online criminals.
• Be alert when you download and install freeware, open-source software, or shareware. Avoid downloading and installing browser extensions and applications you are not knowledgeable about.
• Always download software from reliable sources like official sites as opposed to untrustworthy sharing space. Avoid torrents and peer-to-peer clients.
What To Do If You Cannot Download Safebytes Anti-Malware?
All malware is bad, but certain types of malware do much more damage to your PC than others. Some malware sits in between your computer and the net connection and blocks some or all internet sites that you really want to check out. It will also block you from installing anything on your PC, especially anti-malware applications. So what to do when malicious software keeps you from downloading or installing Safebytes Anti-Malware? Although this type of issue will be tougher to get around, there are some actions you can take.
Install the antivirus in Safe Mode
In Safe Mode, you can adjust Windows settings, un-install or install some software, and get rid of hard-to-delete viruses. In the event the virus is set to load immediately when PC starts, shifting into this mode may well prevent it from doing so. In order to get into Safe Mode or Safe Mode with Networking, press the F8 key while the PC is booting up or run MSConfig and look for the “Safe Boot” options under the “Boot” tab. Once you’re in Safe Mode, you can try to install your antivirus program without the hindrance of the virus. Now, you can run the anti-malware scan to eliminate computer viruses and malware without any hindrance from another malicious application.
Download the antivirus software using a different browser
Some viruses might target vulnerabilities of a specific browser that block the downloading process. If you suspect that your Internet Explorer happens to be hijacked by a virus or otherwise compromised by cybercriminals, the best approach is to switch over to an alternate web browser like Chrome, Firefox, or Safari to download your chosen security software – Safebytes Anti-Malware.
Make a bootable USB anti-virus drive
Here’s another solution which is creating a portable USB anti-virus software that can scan your system for malware without the need for installation. Follow these steps to run the anti-virus on the affected PC.
1) Download Safebytes Anti-Malware or Windows Defender Offline onto a clean computer.
2) Plug the USB drive into the uninfected PC.
3) Double-click on the downloaded file to open the installation wizard.
4) Choose the drive letter of the flash drive as the place when the wizard asks you exactly where you would like to install the anti-virus. Follow the on-screen instructions to complete the installation process.
5) Now, transfer the pen drive to the infected PC.
6) Double-click the EXE file to run the Safebytes tool from the flash drive.
7) Press the “Scan Now” button to start the virus scan.
SafeBytes Anti-Malware - More Protection For You
These days, an anti-malware tool can protect the computer from different forms of online threats. But wait, how to choose the right one amongst various malware protection software that is available on the market? Perhaps you might be aware, there are lots of anti-malware companies and products for you to consider. Some of them are good, some are decent, while some will affect your computer themselves! You must be careful not to pick the wrong product, especially if you purchase premium software. When it comes to commercial anti-malware software options, many people opt for popular brands, like SafeBytes, and they are very happy with it.
Safebytes is among the well-established computer solutions firms, which provide this all-inclusive anti-malware software. Using its cutting edge technology, this application can help you eradicate multiples types of malware which includes computer viruses, worms, PUPs, trojans, adware, ransomware and browser hijackers.
SafeBytes has outstanding features when compared with various other anti-malware programs. Below are a few of the great ones:
Real-time Protection: Malware programs aiming to enter the computer are discovered and stopped as and when detected by the SafeBytes active protection shields. It’ll examine your computer system for suspicious activity regularly and shields your personal computer from unauthorized access.
Optimum AntiMalware Protection: Safebytes is built on the best virus engine within the industry. These engines can find and remove threats even during the initial stages of a malware outbreak.
“Fast Scan” Features: SafeBytes’s high speed malware scanning engine lessens scan times and extends battery life. Simultaneously, it’ll effectively identify and remove infected files or any online threat.
Web Filtering: SafeBytes provides instant safety rating to the webpages you are about to check out, automatically blocking harmful sites and to ensure that you’re certain of your online safety while browsing the internet.
Lightweight: SafeBytes is really a lightweight tool. It use up an extremely small amount of processing power as it operates in the background therefore you will not observe any system performance difficulties.
Premium Support: For any technical concerns or product support, you can obtain 24/7 professional assistance via chat and e-mail.
Technical Details and Manual Removal (Advanced Users)
If you don’t wish to use malware removal software and prefer to get rid of Chedot manually, you could possibly do so by going to the Windows Add/Remove Programs menu in the Control Panel and deleting the offending program; in cases of browser extensions, you may uninstall it by visiting the browsers Add-on/Extension manager. It’s also highly recommended to factory reset your browser to its default state to fix corrupt settings.
To make sure of complete removal, find the following registry entries on your computer and delete it or reset the values accordingly. Please keep in mind that only advanced users should try to manually edit the system files mainly because deleting any single critical registry entry results in a major problem or even a system crash. Furthermore, certain malware keeps replicating which makes it tough to get rid of. You’re encouraged to do this procedure in Safe Mode.
 Error Causes
Error Causes
 If we are to believe news from Intel, new series of processors based on Alder Lake architecture are about to be released somewhere in October. Alder Lake is the 12th Generation Core of Intel processors and it is meant to have all advantages of the current CPU structure.
I9 is aimed to pack a punch against its competitors with technology including eight high-performance Golden Cove cores (P-cores) with Hyper-Threading and eight energy-efficient Goldmont (E-cores) equipped with a 30MB L3 cache and operating at high clock speeds.
During the benchmark test, the new CPU outperformed all of Intel’s previous Rocket Lake structure processors which is logically expected but the big surprise came from results that indicate better performance than Apple’s new M1 processor even in single-threaded performance which is supposed to be best in that field.
Another surprise was really beating AMD Ryzen 9 in each field. If we take into account that i9 has 16 cores in total and can process 24 threads against Ryzen 9 with 16 Cores and 32 threads this is an impressive feature.
Now truth to be told Alder lake has massive L3 cache and microarchitectural advantages and consumes much more power but the results of performance are high. Also, note that this early CPU is not really a mass production one and maybe some things will still change but early results are very satisfactory.
We will see what will price tag be since in this age of shortage and competition that will also play a big role in its overall success. Speaking of competition I eagerly await AMD’s response to this, in any way it seems that the CPU market is for some turbulence which is always a good thing for the final customer and I welcome it.
If we are to believe news from Intel, new series of processors based on Alder Lake architecture are about to be released somewhere in October. Alder Lake is the 12th Generation Core of Intel processors and it is meant to have all advantages of the current CPU structure.
I9 is aimed to pack a punch against its competitors with technology including eight high-performance Golden Cove cores (P-cores) with Hyper-Threading and eight energy-efficient Goldmont (E-cores) equipped with a 30MB L3 cache and operating at high clock speeds.
During the benchmark test, the new CPU outperformed all of Intel’s previous Rocket Lake structure processors which is logically expected but the big surprise came from results that indicate better performance than Apple’s new M1 processor even in single-threaded performance which is supposed to be best in that field.
Another surprise was really beating AMD Ryzen 9 in each field. If we take into account that i9 has 16 cores in total and can process 24 threads against Ryzen 9 with 16 Cores and 32 threads this is an impressive feature.
Now truth to be told Alder lake has massive L3 cache and microarchitectural advantages and consumes much more power but the results of performance are high. Also, note that this early CPU is not really a mass production one and maybe some things will still change but early results are very satisfactory.
We will see what will price tag be since in this age of shortage and competition that will also play a big role in its overall success. Speaking of competition I eagerly await AMD’s response to this, in any way it seems that the CPU market is for some turbulence which is always a good thing for the final customer and I welcome it. 
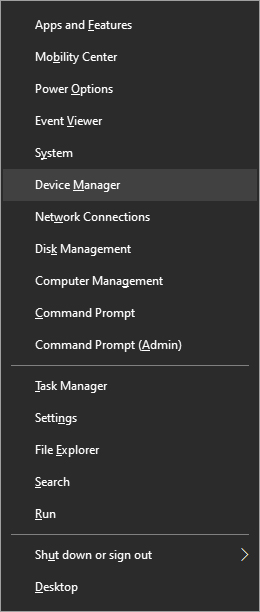
 In the menu choose device manager and click on it.
In the menu choose device manager and click on it.
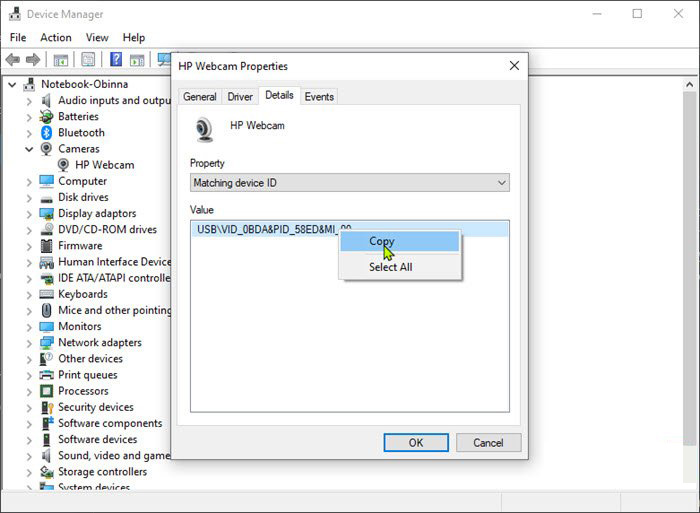
 When the device manager opens, expand the Imaging devices or Cameras section.
Right-click Integrated Camera or the primary webcam, and click Properties.
Go to the Details tab.
Under the Property section, click to select Matching device ID from the drop-down.
Right-click the value and select Copy
When the device manager opens, expand the Imaging devices or Cameras section.
Right-click Integrated Camera or the primary webcam, and click Properties.
Go to the Details tab.
Under the Property section, click to select Matching device ID from the drop-down.
Right-click the value and select Copy
 The next step is to download and install
The next step is to download and install 