Error Code 0xC004F00F – What is It?
Error Code 0xC004F00F can appear during the Windows 10 installation and activation process. It is a fairly straightforward error code that occurs when a product key is entered in that is unable to be used to complete the final activation of the new operating system. This error code is most commonly related to the installation of new pieces of hardware on a machine that was already running Windows 10 at a previous time.
Error Code 0xC004F00F can also appear on other versions of the Windows software, so if you are not specifically trying to install and activate Windows 10 when this message appears, you may want to contact a qualified Windows technician to help resolve your system error, as the error code has different causes and resolution methods on other versions of the Windows operating system.
Solution
 Error Causes
Error Causes
In some cases, Error Code 0xC004F00F will show up if you are attempting to install Windows 10 on a computer in which the hard drive has been replaced or significantly altered. It can also appear when other major pieces of hardware, like the motherboard, have been changed out. These pieces may be changed as part of an upgrade to new or better hardware or be changed due to the malfunction of the original pieces of equipment. Because it may appear to the Windows activation servers that you are attempting to use the same product code that you have used before to activate what appears to be a new machine (even if the machine is the same one, just with some new parts), you may see Error Code 0xC004F00F arise.
Error Code 0xC004F00F can also come up if you have installed Windows 10 on your machine in the past and have already used the product key that you are attempting to use again.
Further Information and Manual Repair
Error Code 0xC004F00F most commonly appears for users who have made major hardware or software changes done on their machine. Because this error specifically arises from the Windows activation servers believing that your computer is a new one, you’ll need to get in touch with the Windows support team in order to resolve the error. From their database, they will be able to confirm that you are not using a new computer and will be able to bypass the error, allowing you to complete the Windows 10 Activation process.
If you haven’t installed or replaced any of the hardware on the computer, but are still seeing Error Code 0xC004F00F arise during your Windows 10 installation, you will still need to get in touch with the Windows support team to bypass the error code.
Calling the Windows' Support Team
When you call into the Windows support team, you’ll want to specifically have a list of the following information readily available: Which pieces of hardware have been changed out on your computer prior to the installation and activation, what method you were using to install Windows 10, which version of Windows 10 that you were attempting to install, whether it was a single-use or multiple-use license, and basic details about your PC like its make, model, and age. You may also want to have the product key that you were attempting to use when Error Code 0xC004F00F first appeared.
By having all of this information ready and on hand ahead of time, you’ll have a greater likelihood that your error will be able to be resolved quickly and efficiently, avoiding long periods spent on the phone with customer service. Make sure that you specifically mention that you are experiencing Error Code 0xC004F00F during the Windows 10 activation process when you call into the Windows support team so that you can be connected to a representative who is equipped to help you resolve this specific problem.
Getting a Qualified Technician
If you are not comfortable in working with the Windows support team or have not been able to successfully resolve Error Code 0xC004F00F even after getting in touch with customer support, contact a qualified technician who is familiar with the Windows 10 activation process and can walk you through the things that you will need to communicate to the Windows support team in order to have them bypass or resolve the error code.
If you wish to always have at your disposal a utility tool to fix these Windows 10 and other related issues when they do arise, download and install a powerful automated tool.



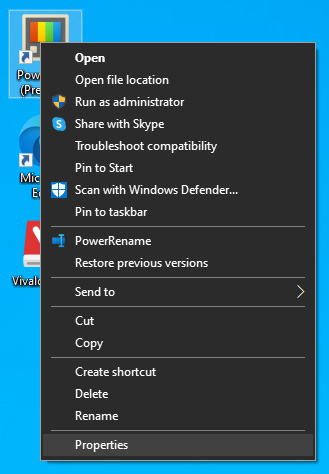 The application settings screen will open, in upper tabs locate Compatibility and left-click on it.
The application settings screen will open, in upper tabs locate Compatibility and left-click on it.
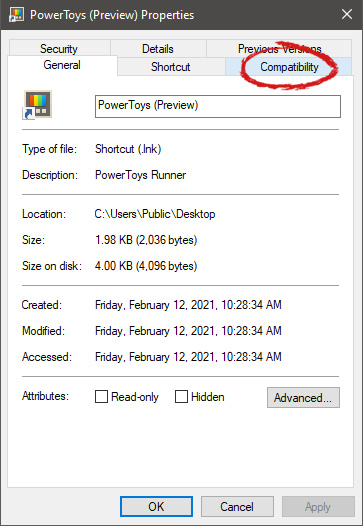 After the click, you will find yourself in application compatibility settings.
After the click, you will find yourself in application compatibility settings.
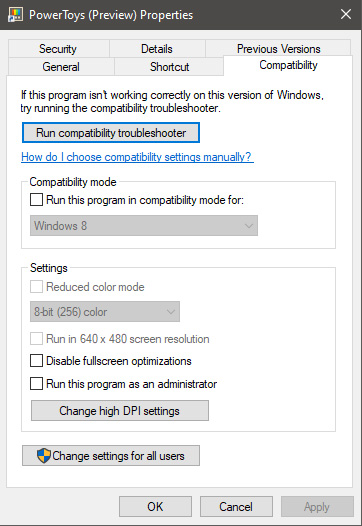 In this window, you will face different options to run the chosen application in various modes in order to make it run. How settings are self-explanatory and different applications will need different settings sadly we can not cover them all but your safest bet is to run them in an environment where they have worked.
For example, if the application was working fine in Windows XP and required administrator privileges, check Run this program as an administrator and Run this program in compatibility mode for Windows XP.
In this window, you will face different options to run the chosen application in various modes in order to make it run. How settings are self-explanatory and different applications will need different settings sadly we can not cover them all but your safest bet is to run them in an environment where they have worked.
For example, if the application was working fine in Windows XP and required administrator privileges, check Run this program as an administrator and Run this program in compatibility mode for Windows XP.