Libcurl.dll - What is it?
Libcurl.dll is a Dynamic Link Library file; a component of Google Earth. Google Earth is a 3D software tool.
Libcurl.dll file is visible within a 3D application with the help of which software users can see satellite images, maps, and other geography-related information from their computers.
The Libcurl.dll file enables users to map the earth using superimposing images received via satellite imagery and also aerial photography. However, Libcurl.dll error messages may occur while using or installing this program.
The libcurl.dll error message is displayed in either of the following formats:
- "Cannot find [PATH]libcurl.dll"
- "The file libcurl.dll is missing."
- "Libcurl.dll Not Found"
- "This application failed to start because libcurl.dll was not found. Re-installing the application may fix this problem."
Solution
 Error Causes
Error Causes
Libcurl.dll may occur due to several reasons. These include:
- Bugged program
- Viral infection may add malicious codes to Libcurl.dll file and generate error messages
- Registry issues
- Missing libcurl.dll file
- Hard disk failure
- Misconfigured system files
If you experience difficulty in using Google Earth and come across libcurl.dll error message, it is advisable to resolve the error immediately typically because this error has severe consequences.
If not fixed timely, it can lead to the blue screen of death errors, system hang-ups and freezes, sluggish PC performance, PC crashes and browser crashes, slow internet speed, and other system errors.
Further Information and Manual Repair
This error is crucial but the good news is that it is easy to fix. To resolve it, you don’t have to hire a technical expert and pay hundreds of dollars.
You can repair the issue with ease by yourself regardless of whether or not you are technically sound. Continue reading to find out the best solutions to fix libcurl.dll error code on your system without any hassle.
Here are some of the easiest and the best methods to resolve libcurl.dll error:
1. Check your recycle bin
Since .dll files are shared by multiple programs, there is a possibility that you might have accidentally deleted libcurl.dll file when uninstalling a certain program on your system which was also sharing this file.
And because of this, you may experience the missing libcurl.dll error message. To resolve it, all you have to do is to
check your recycle bin. If you find the file here, restore it. Once restored, try running the program again! If the error code does not appear, then this means it is resolved.
However, if it continues to persist, then try other solutions given below.
2. Scan for Malicious Software on your System
While downloading files and checking unknown emails malicious software like viruses, malware and spyware can also enter your PC.
Such software can damage and corrupt dll files. This could be the underlying cause of libcurl.dll error on your PC too. So, to resolve the issue, scan and remove
malicious viruses and spyware from your system by using a powerful anti-virus.
However, please note, anti-viruses are notorious for slowing PC performance and also sometimes you may also have to stop all other activities on your PC.
3. Clean the Cluttered Disk, Repair dll files and Restore the Registry
Libcurl.dll file error may also occur due to hard disk failure. This triggers registry issues. If you don’t clean the registry every now and then, it overloads the hard disk with files.
These include both important and unnecessary files like internet history, temporary files, cookies, junk files, invalid registry entries, and bad keys. These clutter the disk, damaged dll files, and the registry.
Therefore first you need to clean the cluttered disk, repair libcurl.dll files and restore the registry. Executing it manually can take a lot of time as you may find it complex if you are not a computer programmer. However, the best, easiest, and quickest way to clean, repair, and restore the registry is to download Restoro
Why Restoro?
Restoro is an innovative, advanced, and multi-functional PC repair tool loaded with powerful and PC performance boosting utilities including an intuitive registry cleaner, an antivirus, Active X controls, and class module, and a system optimizer.
So, whether the libcurl.dll error message is triggered by a viral infection, hard disk failure, or registry issues, this tool takes care of all!
The registry cleaning feature scans all registry issues, cleans the hard disk by removing unnecessary and obsolete files, repairs damaged and corrupt dll files, and restores the registry thereby resolving libcurl.dll error in seconds.
Simultaneously, the antivirus utility removes viruses and malware if found. And the system optimizer feature ensures optimum PC performance.
Restoro is easy to navigate and operate. It is user-friendly, safe, bug-free, and efficient. Furthermore, it is compatible with all Windows versions.
Click here to download Restoro and repair your PC and resolve libcurl.dll error today!





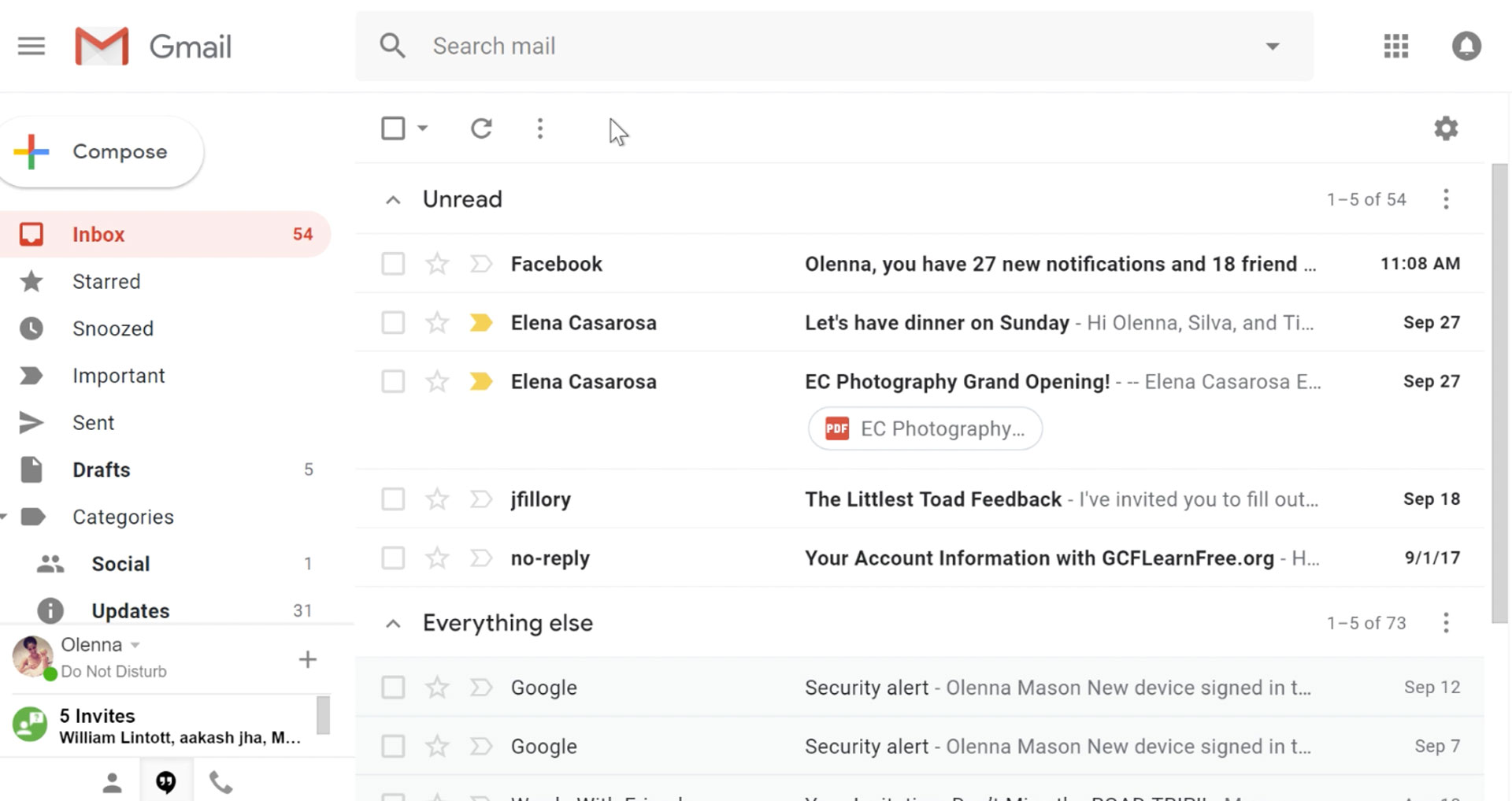 It would be very difficult to even start a free eMail list without mentioning Google's Gmail. Introduced all the way back in 2004 as an invite-only service it became over time the most popular email platform largely due to the fact Google is offering free eMail accounts.
There are a lot of good things to be said about Gmail itself, most of the area is clutter-free and the largest space is reserved for eMail itself letting users focus on what is important. WEB client itself means that you do not need to have any application installed on your device, altho via Google chrome, you can use Gmail offline offering you flexibility if needed.
The ability to connect and manage other accounts like Outlook, Yahoo, etc is just making Gmail even more attractive, and the snooze feature is a really neat little detail that will pause eMail notifications if you need to focus on other things.
Lack of organizing messages into folders is a little confusing since Gmail offers its own unique label system but sometimes I need to have old reliable save eMail to folder.
All in all, Gmail is a great service and it offers a great eMail on the go experience.
It would be very difficult to even start a free eMail list without mentioning Google's Gmail. Introduced all the way back in 2004 as an invite-only service it became over time the most popular email platform largely due to the fact Google is offering free eMail accounts.
There are a lot of good things to be said about Gmail itself, most of the area is clutter-free and the largest space is reserved for eMail itself letting users focus on what is important. WEB client itself means that you do not need to have any application installed on your device, altho via Google chrome, you can use Gmail offline offering you flexibility if needed.
The ability to connect and manage other accounts like Outlook, Yahoo, etc is just making Gmail even more attractive, and the snooze feature is a really neat little detail that will pause eMail notifications if you need to focus on other things.
Lack of organizing messages into folders is a little confusing since Gmail offers its own unique label system but sometimes I need to have old reliable save eMail to folder.
All in all, Gmail is a great service and it offers a great eMail on the go experience.
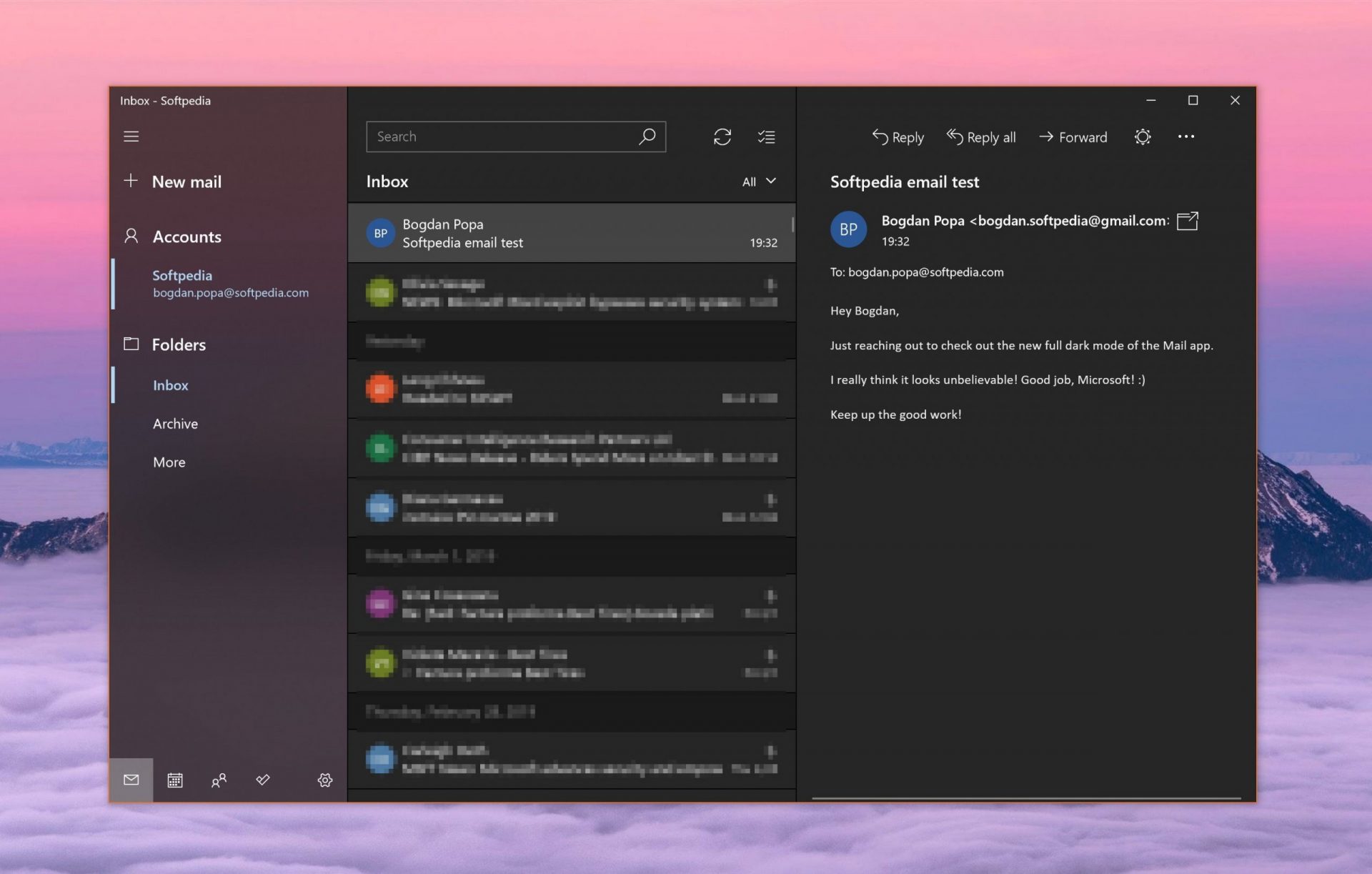 Free Windows eMail client simply called Mail is what was once outlook express. Mail itself has the ability to work with other popular accounts like Google Gmail account, Yahoo, iCloud etc. How it comes with Windows OS and it integrates very well with Microsoft Calendar, this eMail client is for many the first choice.
On the negative side, I might say this is a strip-down version of Outlook which is paid solution so some features are missing if we would compare the two.
Overall, a simple and nice eMail client worth your time, especially if you are on the Windows platform.
Free Windows eMail client simply called Mail is what was once outlook express. Mail itself has the ability to work with other popular accounts like Google Gmail account, Yahoo, iCloud etc. How it comes with Windows OS and it integrates very well with Microsoft Calendar, this eMail client is for many the first choice.
On the negative side, I might say this is a strip-down version of Outlook which is paid solution so some features are missing if we would compare the two.
Overall, a simple and nice eMail client worth your time, especially if you are on the Windows platform.
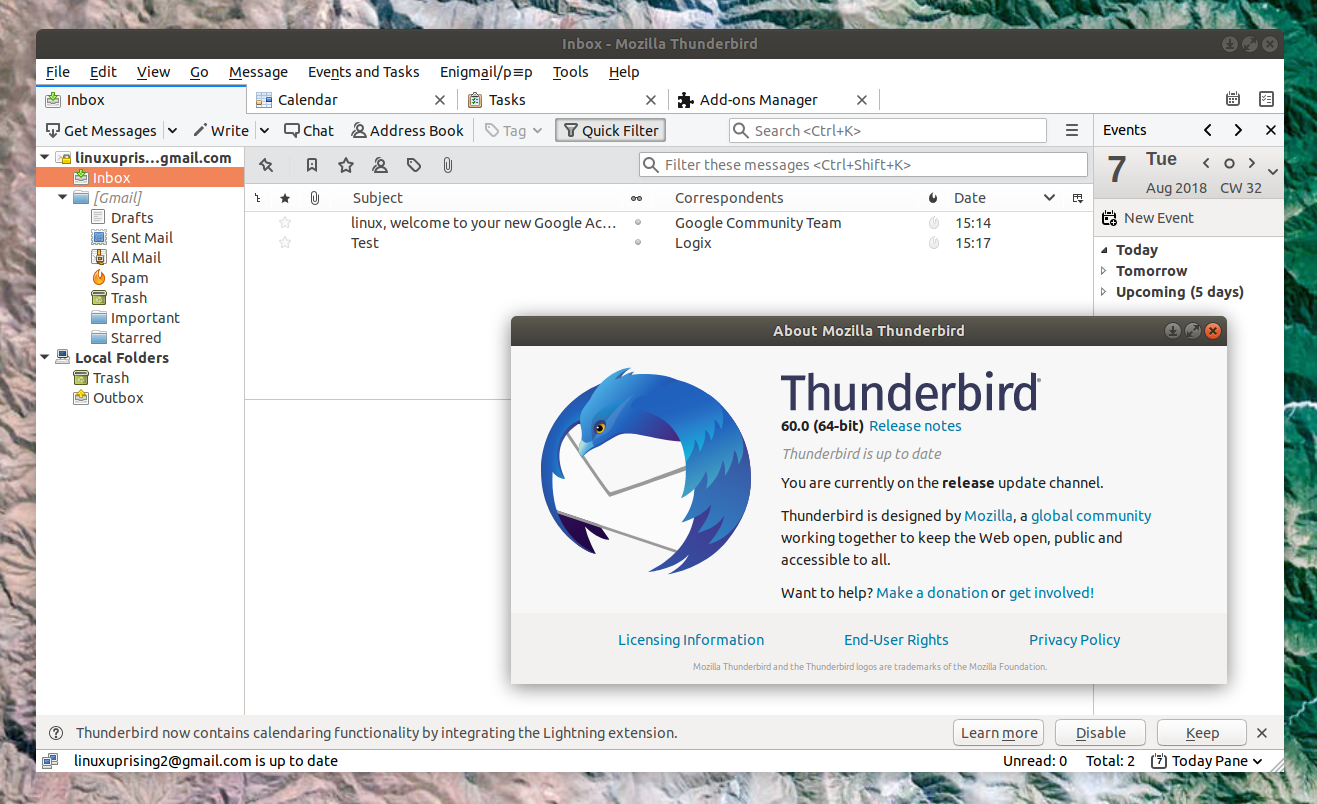 Great eMail client matching in functions against paid and premium solutions of big tech companies. Fueled with plenty of customization options and reskinning ones this eMail client offers a lot for its free price tag.
It is also fueled by Mozilla community focusing on privacy and security. It can work with any mail service and it is lightweight with a clean look, altho the look itself can be heavily customized.
The bad side is that client itself relies on email services to provide cloud-based emails, so if you are receiving your email via a service that does not have a cloud-based service in itself all of your received emails will be locked to the computer where you have received them. Also customizing it can be sometimes a little too technical for the average computer user.
All in all, Thunderbird is one great eMail client and it would be a shame not to use it because of its technical side, if you need a reliable and secure eMail client on a single machine, look no further than Thunderbird.
Great eMail client matching in functions against paid and premium solutions of big tech companies. Fueled with plenty of customization options and reskinning ones this eMail client offers a lot for its free price tag.
It is also fueled by Mozilla community focusing on privacy and security. It can work with any mail service and it is lightweight with a clean look, altho the look itself can be heavily customized.
The bad side is that client itself relies on email services to provide cloud-based emails, so if you are receiving your email via a service that does not have a cloud-based service in itself all of your received emails will be locked to the computer where you have received them. Also customizing it can be sometimes a little too technical for the average computer user.
All in all, Thunderbird is one great eMail client and it would be a shame not to use it because of its technical side, if you need a reliable and secure eMail client on a single machine, look no further than Thunderbird.
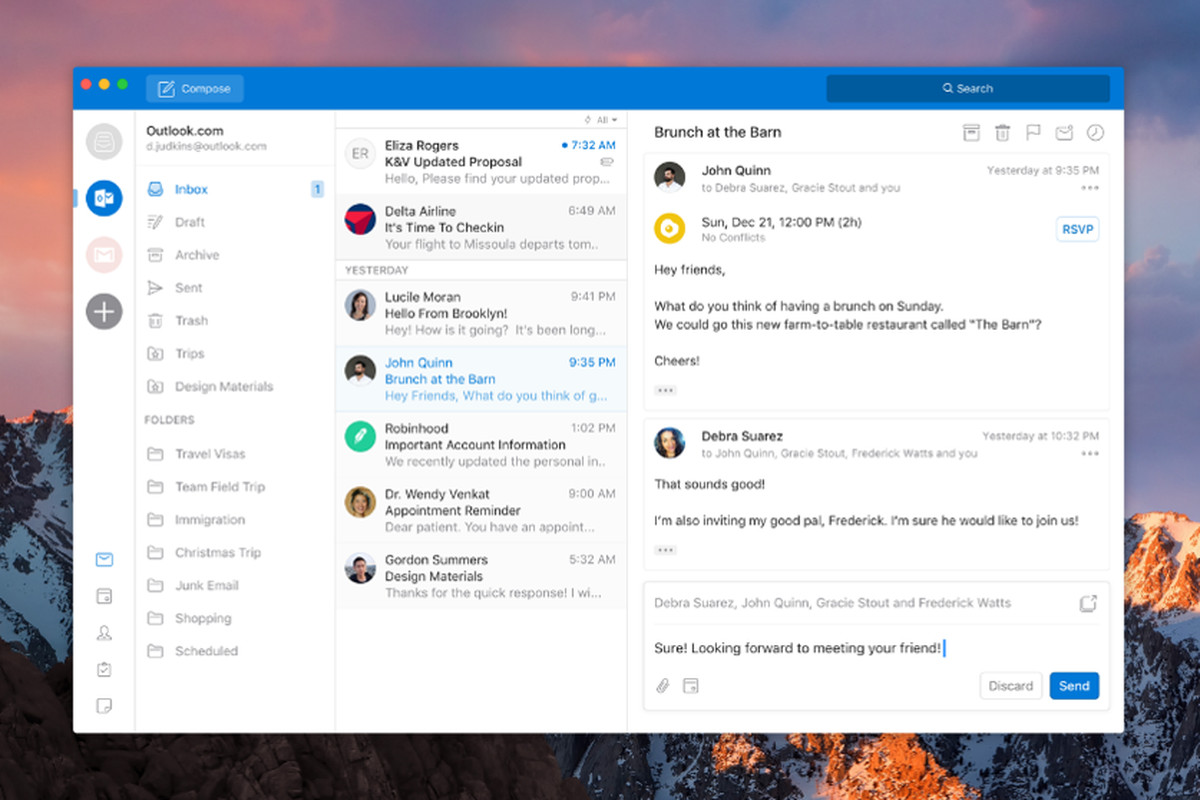 Outlook comes as a part of the Microsoft Office suite and as one of the oldest eMail clients, it is still widely popular and adopted through many users and businesses. It has tight integration with all Microsoft services and full integration with Calendar making it one of the if not the best eMail client out there.
Outlook also has a free online service completely free for personal use as well.
The downside is that you can not get it as a separate product if you want a business version other than as a part of the Office suite.
The final verdict would be that this is perhaps the best eMail client out but the big downside is that there is no desktop version outside the Office suite.
Outlook comes as a part of the Microsoft Office suite and as one of the oldest eMail clients, it is still widely popular and adopted through many users and businesses. It has tight integration with all Microsoft services and full integration with Calendar making it one of the if not the best eMail client out there.
Outlook also has a free online service completely free for personal use as well.
The downside is that you can not get it as a separate product if you want a business version other than as a part of the Office suite.
The final verdict would be that this is perhaps the best eMail client out but the big downside is that there is no desktop version outside the Office suite.
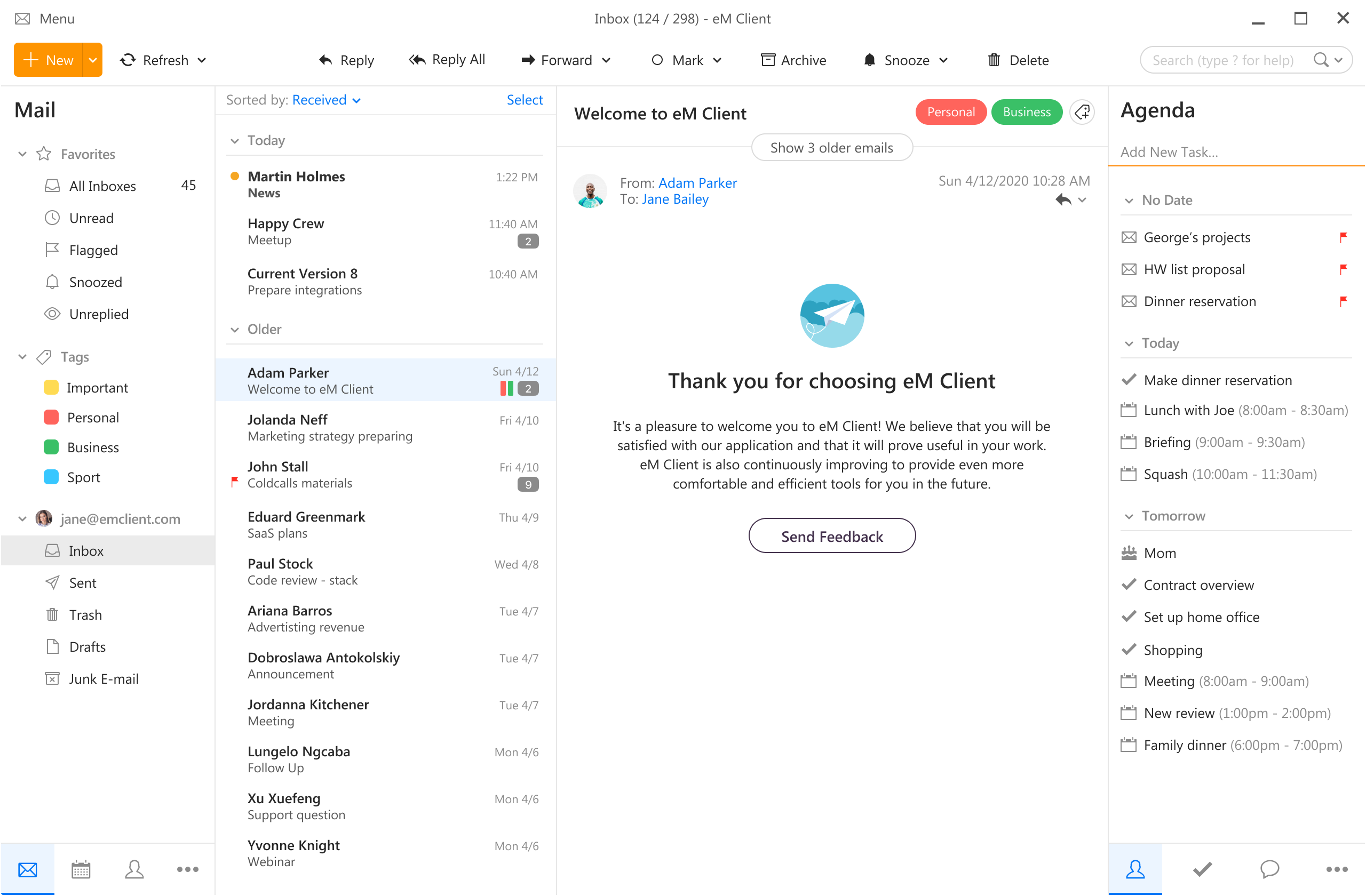 eM Client offers a wide array of features, including a calendar, contacts, and chat. Support is provided for all the major email services including Gmail, Yahoo, iCloud, and Outlook.com. The latest version also offers PGP encryption, live backup, basic image editing capabilities, and auto-replies for Gmail.
Its automatic system makes it very easy to get emails from other services since there is no manual setting, all that is needed is to type in your email and eM Client will do everything else automatically.
A one-time purchase is not pricy and it could offer some features that some free clients are missing. Go check it out with a free trial and see if it is for you.
eM Client offers a wide array of features, including a calendar, contacts, and chat. Support is provided for all the major email services including Gmail, Yahoo, iCloud, and Outlook.com. The latest version also offers PGP encryption, live backup, basic image editing capabilities, and auto-replies for Gmail.
Its automatic system makes it very easy to get emails from other services since there is no manual setting, all that is needed is to type in your email and eM Client will do everything else automatically.
A one-time purchase is not pricy and it could offer some features that some free clients are missing. Go check it out with a free trial and see if it is for you.
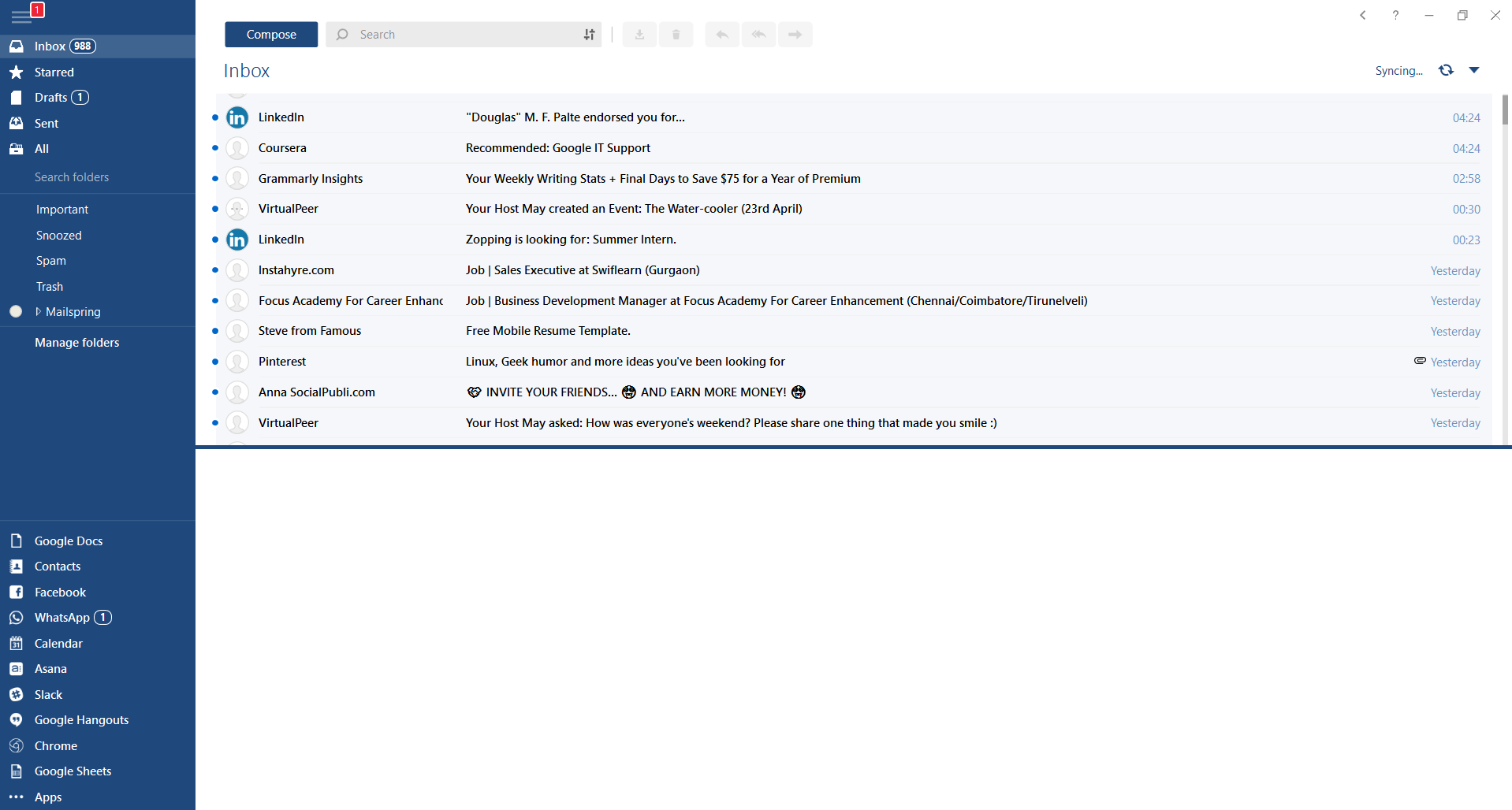 This eMail client's main focus is the simplicity of use with visual appeal while tackling multiple eMail accounts. It has many built-in apps along with a customizable interface. Unlike some more Microsoft-centric email clients, Mailbird Business supports a diverse range of integrated apps, including WhatsApp, Google Docs, Google Calendar, Facebook, Twitter, Dropbox, and Slack, all making for a better-streamlined workflow.
The downside of this client is the yearly subscription plan. I think people, in general, want to get away from software subscription plans so I will include this as a downside but bear in mind it is downside just in terms of a business plan not in the client itself.
This eMail client's main focus is the simplicity of use with visual appeal while tackling multiple eMail accounts. It has many built-in apps along with a customizable interface. Unlike some more Microsoft-centric email clients, Mailbird Business supports a diverse range of integrated apps, including WhatsApp, Google Docs, Google Calendar, Facebook, Twitter, Dropbox, and Slack, all making for a better-streamlined workflow.
The downside of this client is the yearly subscription plan. I think people, in general, want to get away from software subscription plans so I will include this as a downside but bear in mind it is downside just in terms of a business plan not in the client itself.
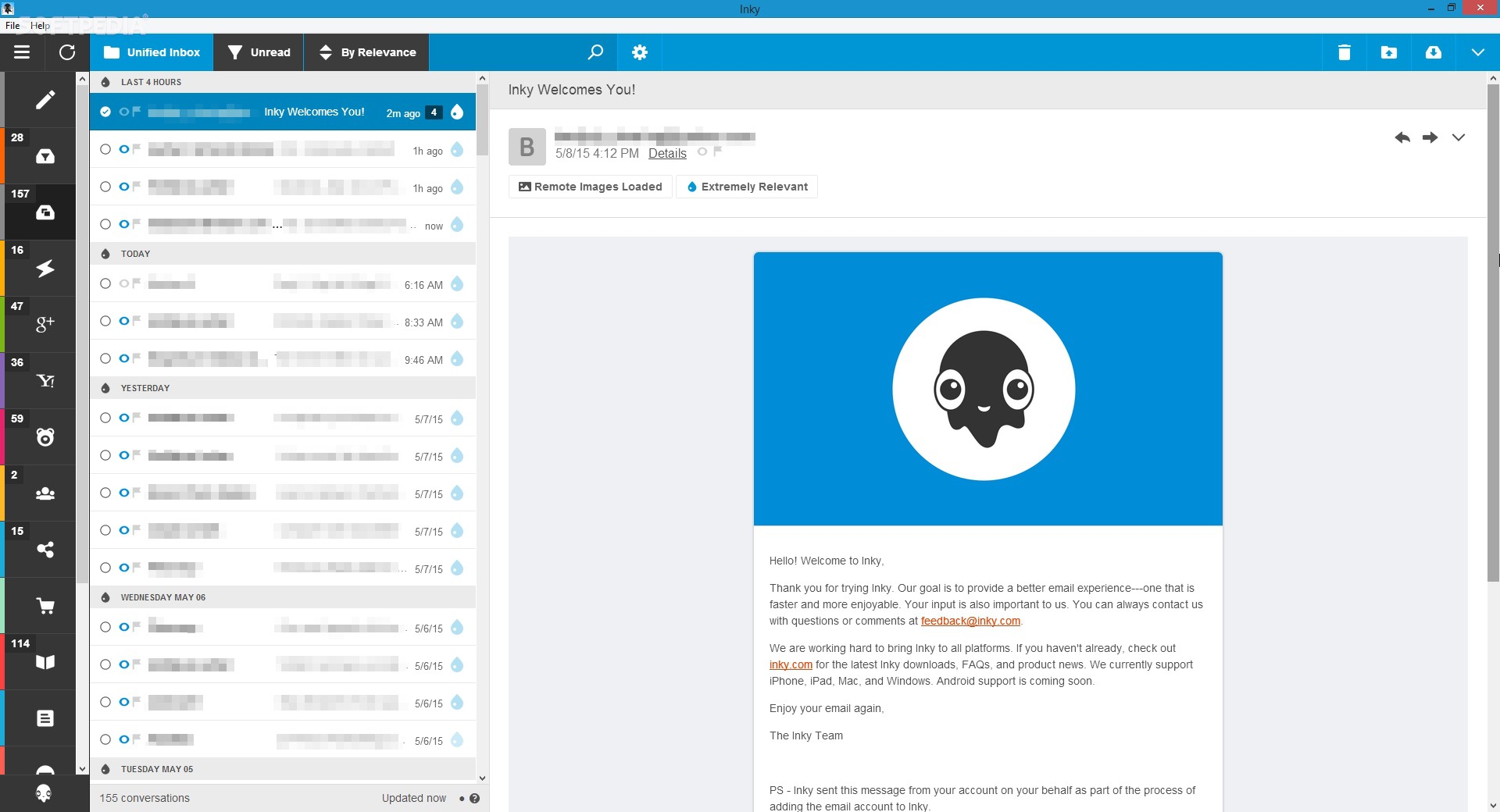 Inky is eMail client if you are looking for security. It uses AI along with machine learning in order to block all types of phishing attacks that can get through to other clients. The proprietary machine learning technology can literally read an email to determine if it has phishing content, and then is able to quarantine the email or deliver it with the malicious links disabled. It also takes things a step further and offers an analytics dashboard, which allows an administrator to see patterns of attacks based on dates, or targeted users.
The downside is that client itself is so much focused on security that sometimes some nonsecurity features get overlooked and provide a poor experience but if you need a good and greatly secured eMail client Inky is one to check out.
Inky is eMail client if you are looking for security. It uses AI along with machine learning in order to block all types of phishing attacks that can get through to other clients. The proprietary machine learning technology can literally read an email to determine if it has phishing content, and then is able to quarantine the email or deliver it with the malicious links disabled. It also takes things a step further and offers an analytics dashboard, which allows an administrator to see patterns of attacks based on dates, or targeted users.
The downside is that client itself is so much focused on security that sometimes some nonsecurity features get overlooked and provide a poor experience but if you need a good and greatly secured eMail client Inky is one to check out.  Following a two-year investigation by the California Department of Fair Employment and Housing, the state has filed a lawsuit against Activision Blizzard for fostering a "frat boy" culture in which female employees are allegedly subjected to unequal pay and sexual harassment.
As reported by Bloomberg, Activision Blizzard is being accused by the state of California of discriminating against female employees at nearly all levels of employment, including in regards to compensation, promotion, assignments, and termination. The state alleges Activision Blizzard’s leadership has failed to address any of these outstanding issues or prevent them from occurring within the workplace. You can read the full details of the lawsuit here.
The suit, filed Tuesday in the Los Angeles Superior Court, says Activision Blizzard, which is made up of about 20 percent women, assigns women, and women of color, to "lower paid and lower opportunity levels" with lower starting pay for similar work as their male counterparts.
The documents also accuse Activision Blizzard of fostering a "pervasive 'frat boy' workplace culture in the office. Male employees are said to drink "copious amounts of alcohol" as they make their way through cubicles and "often engage in inappropriate behavior toward female employees."
Male employees are said to come to work hungover, play video games during work "while delegating their responsibilities to female employees, engage in banter about their sexual encounters, talk openly about female bodies, and joke about rape."
The lawsuit also cites one particular incident where a female employee, who was already subjected to intense sexual harassment at the company, committed suicide during a work trip with a male supervisor who allegedly brought inappropriate, sexual items with him on the trip.
The lawsuit is asking for an injunction that will force Activision Blizzard to comply with workplace protections, as well as deliver unpaid wages, pay adjustments, back pay, and lost wages and benefits for female employees.
Following a two-year investigation by the California Department of Fair Employment and Housing, the state has filed a lawsuit against Activision Blizzard for fostering a "frat boy" culture in which female employees are allegedly subjected to unequal pay and sexual harassment.
As reported by Bloomberg, Activision Blizzard is being accused by the state of California of discriminating against female employees at nearly all levels of employment, including in regards to compensation, promotion, assignments, and termination. The state alleges Activision Blizzard’s leadership has failed to address any of these outstanding issues or prevent them from occurring within the workplace. You can read the full details of the lawsuit here.
The suit, filed Tuesday in the Los Angeles Superior Court, says Activision Blizzard, which is made up of about 20 percent women, assigns women, and women of color, to "lower paid and lower opportunity levels" with lower starting pay for similar work as their male counterparts.
The documents also accuse Activision Blizzard of fostering a "pervasive 'frat boy' workplace culture in the office. Male employees are said to drink "copious amounts of alcohol" as they make their way through cubicles and "often engage in inappropriate behavior toward female employees."
Male employees are said to come to work hungover, play video games during work "while delegating their responsibilities to female employees, engage in banter about their sexual encounters, talk openly about female bodies, and joke about rape."
The lawsuit also cites one particular incident where a female employee, who was already subjected to intense sexual harassment at the company, committed suicide during a work trip with a male supervisor who allegedly brought inappropriate, sexual items with him on the trip.
The lawsuit is asking for an injunction that will force Activision Blizzard to comply with workplace protections, as well as deliver unpaid wages, pay adjustments, back pay, and lost wages and benefits for female employees.

