 Despite popular belief, there are a lot of users running Linux OS. Linux offers great security and working environment and 96.3% of the world's top 1 million servers run on Linux. 90% of all cloud infrastructure operates on Linux and practically all the best cloud hosts use it. But gaming on Linux is limited, enter Steam proton a Valve’s gaming solution.
Despite popular belief, there are a lot of users running Linux OS. Linux offers great security and working environment and 96.3% of the world's top 1 million servers run on Linux. 90% of all cloud infrastructure operates on Linux and practically all the best cloud hosts use it. But gaming on Linux is limited, enter Steam proton a Valve’s gaming solution.
Proton is a WINE fork with some extra capabilities, to play games and run applications not native and not made to run natively under Linux OS. It is supposed to bridge the Gaming issues for PC users and let them more freedom in choosing an operating system to game on.
Although there are a lot of titles that nowadays run natively on Linux some will still need proton in order to run at all and sadly some of them will not be able to run on Linux even via proton but seeing how Valve is busy and it is trying to push its ideas and technology slowly this gap is closing.
In order to see how the game you want to play performs and behaves on Linux and proton environment visit https://www.protondb.com/ and find out. As soon as the site loads you will be greeted with statistics and a search option to find out the status of the desired game with one of the given statuses: Borked, Bronze, Silver, Gold, Platinum, and Native.
As you probably guessed native means that the game will work on Linux out of the box and borked will probably not work at all. Platinum and gold status means that game will run on proton without any input or tweaks from the user while silver and bronze means that it will work but might need some tweaks in order to make it work.
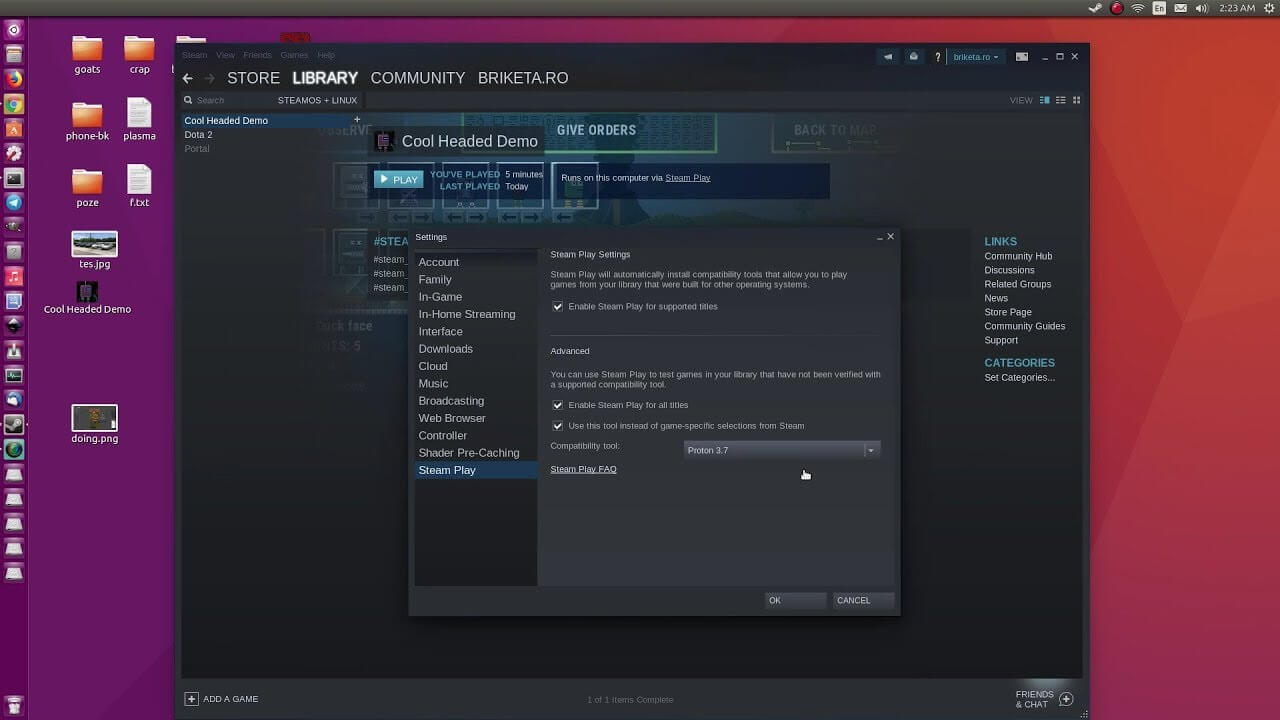
In order to run games under proton inside Linux, you will need firstly a Steam client which luckily works naturally on Linux. Unlocking/activating Steam Proton on your Linux-based system is easy. Just head over to Steam > Settings > Steam Play and toggle the option “Enable Steam Play for Supported Titles”.
Valve has tested and fixed some Steam titles and you will now be able to play those titles. However, if you wish to go even further beyond, and play titles that even Valve has not tested, toggle the option “Enable Steam Play for all titles”.
Even we are not there yet, native gaming on Linux is gaining a foothold each day. Will Steam’s OS with proton technology be one that will turn the tide from Windows or some other tech we cannot tell but one thing is for sure, more choices mean better products so I am hopeful for a bright future.

The Gardening Enthusiast toolbar is another product that is advertised as a helpful addition to your browsing experience when it is really nothing more than the software you should remove as soon as possible. It is touted as a toolbar that will provide you with a lot of useful gardening tips. That is the hook to get you to install it. But, in truth, the only thing that it does is provide you with links to popular gardening websites that you can easily find on any search engine.
When installed the extension will change your default search engine and home page to MyWay.com
While browsing the internet with this extension you will see additional sponsored ads and links throughout your browsing session.
Anti-virus applications have marked this extension as a Browser Hijacker and are therefore marked for removal. While not considered malware, the fact that many users find it to hinder browser performance has led to its detection and flag for optional removal.
diskpartStep 5: Afterwards, type in either of the following commands to help you in either listing all the Disk connects or all the partitions on those disks formed.
diskpart or list volumeStep 6: Next, you need to select any of the two given commands below depending on the list you entered on the previous step.
select disk # or select volume #Step 7: After you enter the command, it will select the Disk or the Partition you want to select. Now you have to type and enter the following command to clean your drive.
cleanStep 8: Now enter any of the two following commands.
list disk or list volumeStep 9: Then type the next command below to create a specified partition.
create partition primaryStep 10: Once done, type in the following command to select the newly created partition.
select partition 1Step 11: Next, type the following command to mark the selected partition as active.
activeStep 12: Finally, restart your computer to successfully apply the changes made and then see if it has fixed the problem or not.
Sadooma is a Browser Extension for Google Chrome. This extension offers users the ability to search for any trending news on the web.
This extension changes your default search engine to Yahoo, and while active it changes the displayed ads on your browser, allowing it to make revenue on every ad you click. While this is not inherently malicious, the extension redirects your search to its servers first before forwarding it to yahoo and displaying search results. The information that is sent back to the servers contains your browsing data & visited web pages. As this represents a security and privacy risk, Sadooma is classified as a browser hijacker for its potentially unwanted functions and poor user experience. From the Author:We’ve got what you need! If you are like us, addicted to interesting viral content, you’ve reached the best place for this. Sadooma will help you to find what is trending right now on the internet in an easy and immediate way. Privacy – We don’t share your information with others. Trending Content – New viral content every day Up to Date – We update sources to keep things fresh. Made with Love – Our content is safe and suitable for all ages.
 Error Causes
Error Causeswmic path SoftwareLicensingService get OA3xOriginalProductKeyTake note of the product key and then proceed to the options given below.